Cyberattacks on the manufacturing and production industry rose by over 52% in 2022 from 2020. Our cybersecurity experts believe that the industry is now more vulnerable than ever to account compromises and supply chain attacks. In addition, the switch to a remote working culture has led to the widespread adoption of cloud technologies but has also created loopholes and weak points that cybercriminals could leverage.
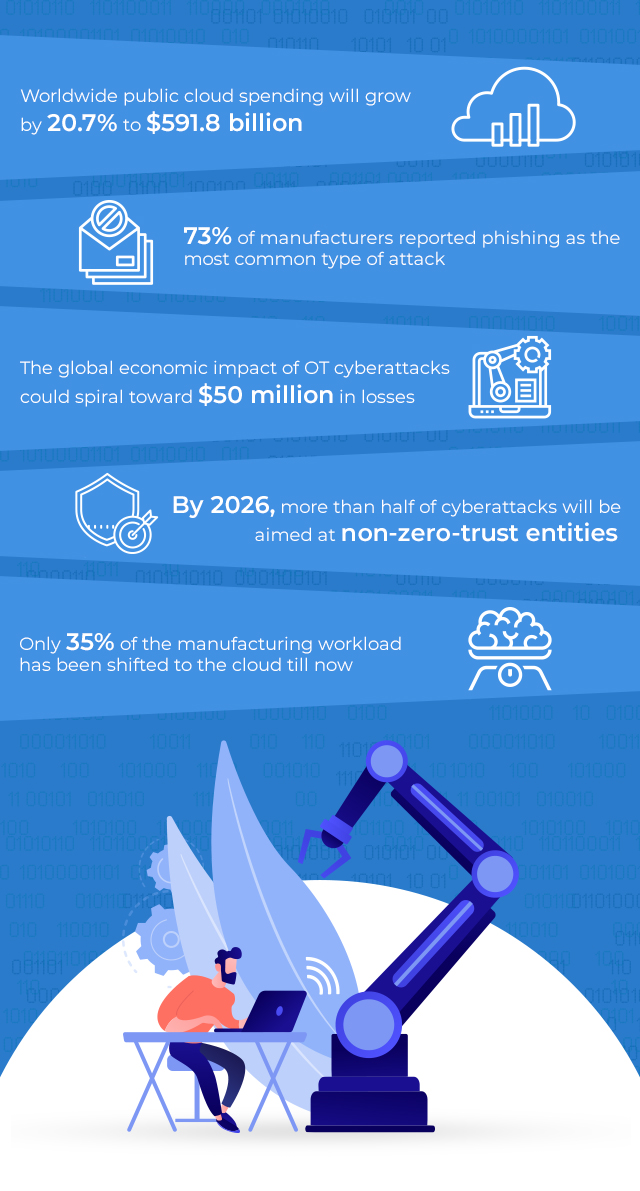
One of the most competitive industries, manufacturing faces a wide range of challenges. Numerous global manufacturers still need to rely on legacy systems that cannot accommodate modern security measures. Manufacturing companies also lack the required security expertise and have a low tolerance for disruption. This makes them a favorite target for cybercriminals. While 41% of average workloads have already been shifted to the cloud globally, the same for manufacturing is only 35%. One of the prime reasons for this is a lack of budget.
The accelerating pace of Operational Technology (OT)- Information Technology (IT) convergence is yet another factor that cannot be overlooked. The overlapping personnel, resources, strategies, and processes result in multiple security weak points and vulnerabilities. Unfortunately, many manufacturers are ill-equipped to navigate these challenges and keep pace with changing industry standards, jeopardizing their security and making achieving long-term goals an uphill task.
As the manufacturing sector gets more digitally connected, design files, quotes, orders, tasks, and labels, nothing will be safe from the clutches of rogue elements. The recent ransomware attacks on Bridgestone Americas, leading them to disconnect their network and halt production completely, is a lesson for all. Therefore, manufacturers increasingly rely on cloud technologies to safeguard mission-critical assets and networks and ensure data security. This calls for a comprehensive approach to data security featuring versatile cybersecurity systems that facilitate predictive monitoring and real-time cyber defense. In addition, a zero-standing privilege is pivotal to tackling such cyber threats, as it follows a request-based account creation and deletes them immediately post-task completion.
So how can organizations successfully leverage security measures while relying on cloud technologies for data security:
-
Designate roles for employees and restrict their access to systems, for instance, segregating duties for highly sensitive systems. This can help reduce risk exposure and prevent cyberattacks from causing business disruption.
-
Ensure employees are thoroughly trained for system interaction, cyber safety best practices, and storing activity logs.
-
Consistently updating secure backups and carrying out regular patches and software-system updates to minimize downtime in the event of a breach.
-
Having a solid disaster recovery backup plan in place to mitigate risks, manage losses, and investigate breaches thoroughly.
The industry 4.0 landscape is witnessing the rise of IT-OT convergence, and the implementation of the 5G technology is also gaining pace. Message Queueing Telemetry Transport (MQTT) protocol is preferred with its lightweight capacity to manage low-footprint data demands of IoT devices. Even IT managers find it convenient to work alongside the same on traditional cloud/on-premise servers. This improves the cyber posture in multi-cloud environments, as visibility is the most significant advantage that can be leveraged through this amalgamation of technologies. For instance, a comprehensive inventory of configuration data collated from various data points within legacy Industrial Control Systems (ICS), including I/O cards, firmware, installed software, and control strategies, can be gathered into a single repository. This reduces cyber risk exposure and increases resiliency through readily accessible and analyzable data. Manufacturing units could also establish a security baseline, monitor unauthorized changes, automate closed-loop management, and regulate requisite compliance.
AI-powered real-time data processing is a boon to the manufacturing sector. Automating repetitive, sensitive, and safety-first tasks helps improve operational excellence and turnaround time, e.g., automating temperature control across warehouses according to outside weather conditions and special storage requirements for different commodities. It can also help reduce wastage, carbon emissions, and input costs. Going a step further, this automation improves worker safety and the overall safety of the organizations, boosting their bottom lines.
Our cybersecurity consultants have found that manufacturing units have partnered with multiple cybersecurity service providers to meet their various security needs for many years. This has led to disparate solutions, siloed processes, and overlapping technologies that enhance exposure to cyber vulnerabilities, which are often taken advantage of by cybercriminals. A significant shift to address this challenge is being seen currently, with manufacturers supporting vendor consolidation and a single-point optimization of security solutions to achieve greater efficiency and enhanced management of security controls. A leading tax, audit, and security provider cites that almost 30% of enterprises are set to adopt various cloud-delivered solutions, such as web gateway, access brokers, and Zero Trust Networks Access (ZTNA) from the same vendor.
These are uncertain times for businesses, and the best way for them to thrive is to leave no stone unturned to ensure a robust security posture. In such a scenario, collaborating with professional security providers can help manufacturers opt for the right security solutions that help them improve security at lower costs.