About Malware
Cybalt observed that with the increase in value and demand for cryptocurrencies, the interest of cybercriminals has also skyrocketed. In general, the malware provides hackers with remote access for using infected systems. The attackers can send spam messages from the infected system to unsuspicious target(s) and adversely influence the infected network. The DoubleFinger malware engages a multilevel attack method, resembling an advanced persistent threat (APT). It initiates with a malicious email attachment and activates a series of events.
DoubleFinger Malware
The cybersecurity experts at Cybalt have researched and found that there is a team of cybercriminals that aids in the theft of cryptocurrencies by using DoubleFinger loader. There are multiple levels that facilitate this cyberattack, including the deployment of DoubleFinger on the targeted systems. It all begins when the user opens the weaponized PIF attachment in an email.
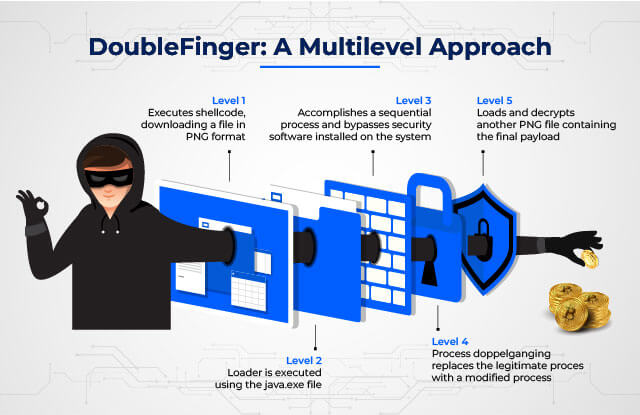
As the cyberattack is a multilevel attack, the first level involves downloading the encrypted elements using DoubleFinger. It is accomplished by using the image-sharing platform Imgur.com, encapsulated (hidden) as a PNG file. These elements include a loader for the second level. The elements also have a legitimate file, viz., java.exe, along with another PNG file to be used for later levels. Next, the DoubleFinger executes the loader. It does so and bypasses the security software, thereby launching the next level. In the fourth level, DoubleFinger utilizes a method called Process Doppelganging to replace a legitimate process with a modified process, framing the payload for the fifth level. Finally, the crypto stealer is installed to steal the cryptocurrencies. It is often scheduled to run daily, affecting the user’s crypto wallets.
DoubleFinger’s multilevel approach
Note: Graphics team will include a diagram/graphic showing multi-levels
DoubleFinger: A Multilevel Approach
We at Cybalt examined the multilevel involvement leading hackers to steal cryptocurrencies using DoubleFinger malware via a weaponized PIF attachment.
- DoubleFinger level 1
- DoubleFinger level 2
- DoubleFinger level 3
- DoubleFinger level 4
- DoubleFinger level 5
Level 1. At this level, DoubleFinger executes shellcode, downloading a file in PNG format (generally from the image-sharing platform Imgur.com.) Actually, this file is not an image file but contains multiple DoubleFinger elements in encrypted form. These elements are used at successive levels of the cyberattack, compromising cybersecurity. The elements also have a legitimate file, viz., java.exe, along with another PNG file.
Level 2. Here, the DoubleFinger level 2 loader is executed using the java.exe file (DoubleFinger level 1). This execution further implements another shellcode, downloading, decrypting, and launching the third level of DoubleFinger.
Level 3. At this level, DoubleFinger accomplishes a sequential process and bypasses security software installed on the system. Here, the loader also decrypts and launches the fourth level. It is present in the PNG file (DoubleFinger level 1). The security experts at Cybalt observed that this PNG file contains malicious code.
Level 4. Here, a method called Process Doppelganging replaces the legitimate process with a modified process containing the DoubleFinger level 5 payload.
Level 5. At this level, DoubleFinger loads and decrypts another PNG file containing the final payload. This payload corresponds to a cryptostealer, which installs itself on the target system. Furthermore, it is scheduled in the Task Scheduler.
After the DoubleFinger loader’s task is accomplished, malware (GreetingGhoul) comes into action. It not only detects crypto wallet applications but also steals data that can be misused by cybercriminals. With the help of the malware, an interface connection to the cryptocurrency application is accomplished, and the user input is easily intercepted. Eventually, the cybercriminals will conveniently control the crypto wallets of the users so they can withdraw funds.
Precautionary Measures
Cybalt recommends the following precautionary measures to safeguard cyber assets as cryptocurrency continues to be of highest interest to cybercriminals:
- Users must make purchases from trusted sources; for example, hardware wallets must be procured from authorized resellers and/or the manufacturer’s website to avoid fake crypto wallets.
- Users must verify the hardware wallets for any type of tampering. It may include the use of glue, scratches, and/or mismatched wallet components.
- Users must ensure firmware verification. The firmware on the hardware wallet must be legitimate and be the latest version.
- Users must use hot and cold wallets. Hot wallets must be used for current transactions, whereas cold wallets must be used for long-term investments.
- Users must know that the hardware wallet vendor never asks for information related to the recovery of the hardware wallet. Always protect the crypto-related details stored on the device or system.
- Users must ensure the use of strong passwords for the hardware wallet. Don’t use easy passwords or the same password for multiple accounts.
Cybalt suggests that organizations enable their employees to certify for different information systems security certifications. The professionals train the employees on IT security, IT architecture, IT design, and various security control processes. These programs enable organizations to safeguard their cyber assets.
Other Blogs

From Nuclear Centrifuges To Machine Shops: Securing IoT
IoT or ‘the internet of things’ has been around for a lot longer than the buzzword
Read More


Demystifying XDR
As the capabilities of threat actors have increased so have the tools which we utilize to detect and respond to their activities.
Read More


Cybersecurity In A Post Pandemic World
As many cyber security practitioners will tell you, the most imminent and dangerous threat to any network are the employees accessing it.
Read More


